SHCTF 2023 [WEEK 1] PWN
简介
SHCTF - "山河"网络安全技能挑战赛 是由齐鲁工业大学、西安邮电大学、广东海洋大学、长春工程学院、郑州轻工业大学、河南大学、齐鲁师范学院、陕西邮电职业技术学院、陕西工业职业技术学院、商丘师范学院、咸阳师范学院(排名不分先后)等十所高校共同举办的 CTF 比赛。
完结撒花!!!这次比赛收获很大,新生赛往往会让你收获意想不到的知识点,挺好的,人民的好比赛,支持支持,明年再来 -_-,接下来会把比赛分周分享记录下来。
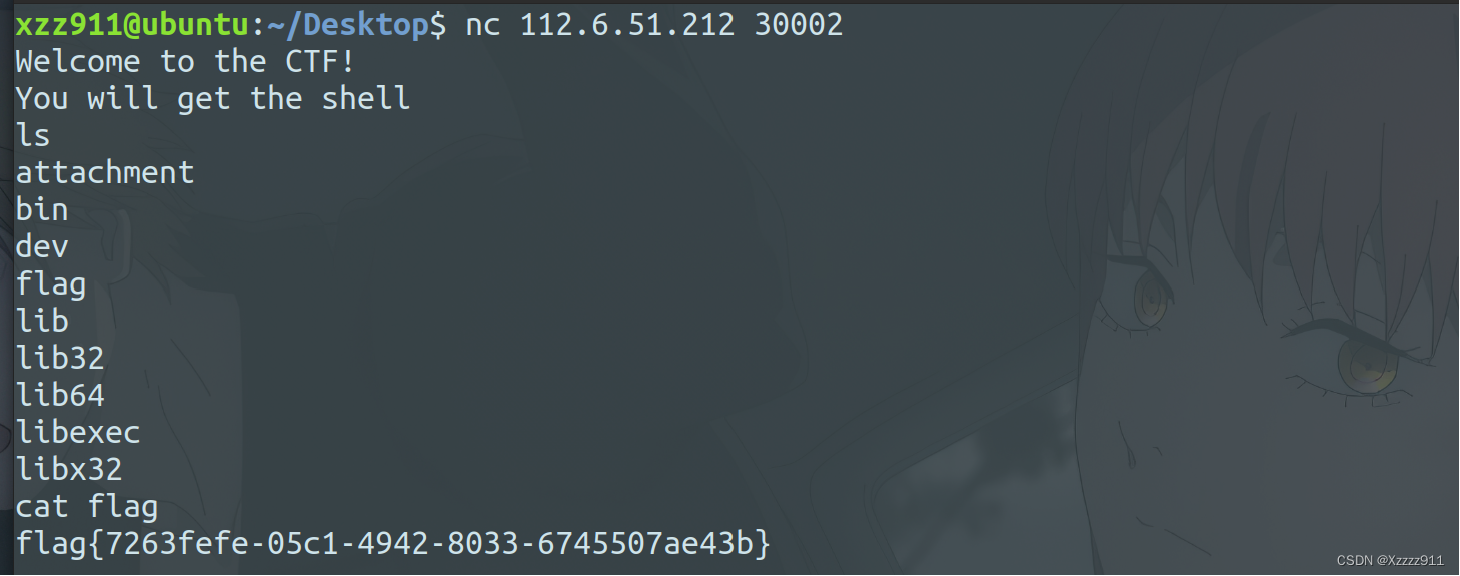
nc
签到题,直接 nc 就完事了。
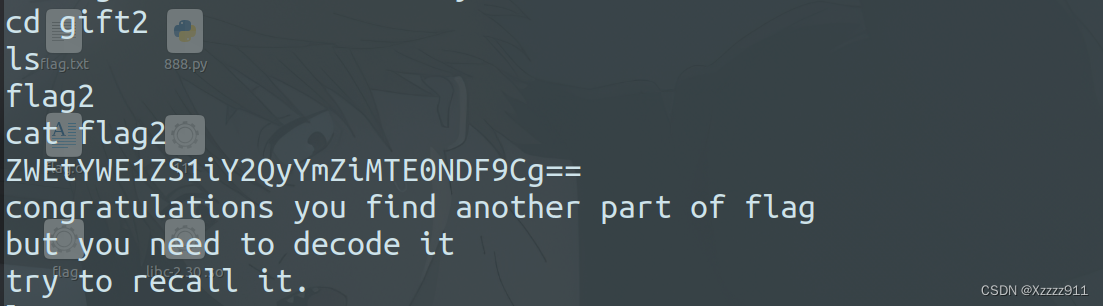
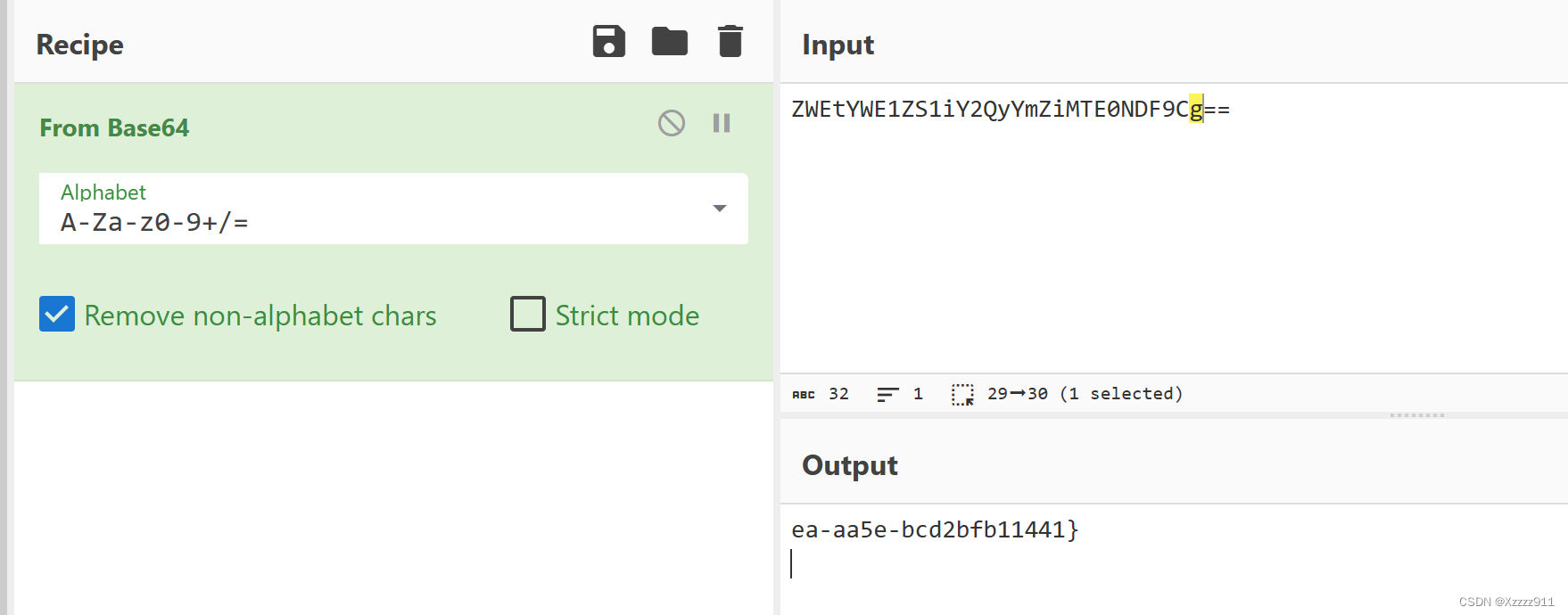
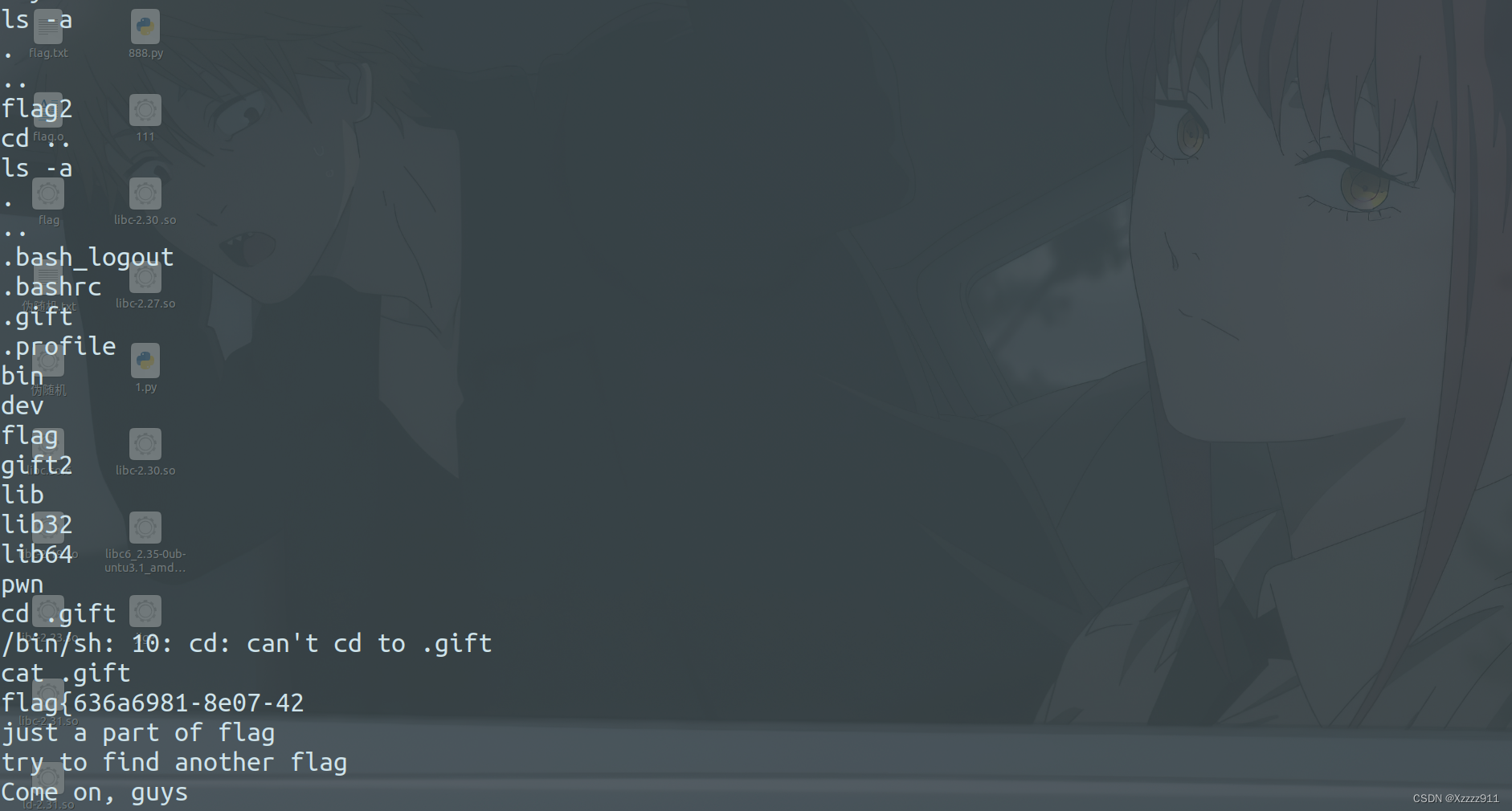
hard nc
签到题,考察隐藏文件的查询(ls -a),然后就是 base64 解码:
flag{636a6981-8e07-42ea-aa5e-bcd2bfb11441} |
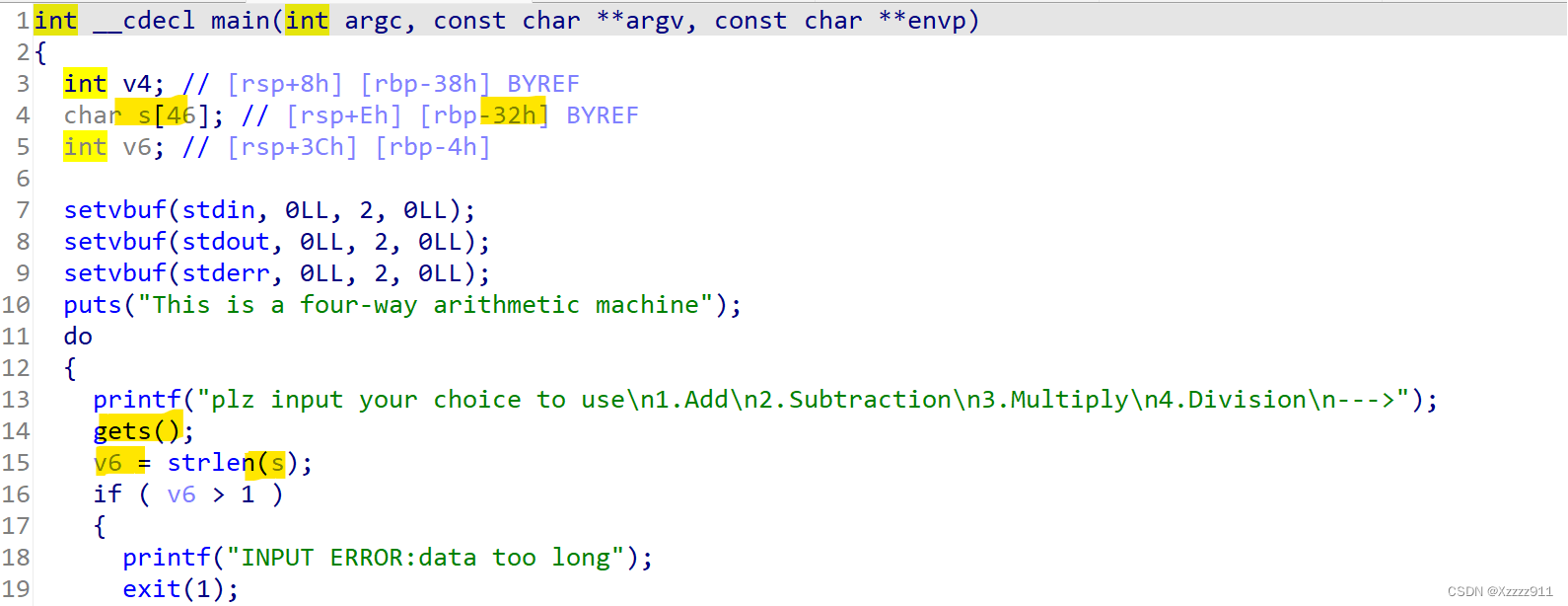
四则计算器
ida反汇编一下,代码审计发现出现了栈溢出,并且还有一个后门函数,想法就是先绕过 if 语句,再调用后门函数,获得shell
exp如下:
from pwn import * |
或者,也可以通过nop滑梯来解决,exp如下:
from pwn import * |
猜数游戏
ida反汇编,代码审计发现有个后门函数 fun11 ,想办法调用后门函数,首先先得绕过 if 函数,输入小于等于11的就行,然后就是想办法跳出while循环,这就需要看 compare 函数,若s与v6相等,则跳出循环,然后就要看到int_num_to_ascii 函数(该函数主要功能是将一个整数转换为ASCII字符数组)将一个随机数转化为ascll码值赋值给v6,并且s是用户输入的值,就可以输入随机数让其等于v6,这样就可以获得shell了,直接干就完事了
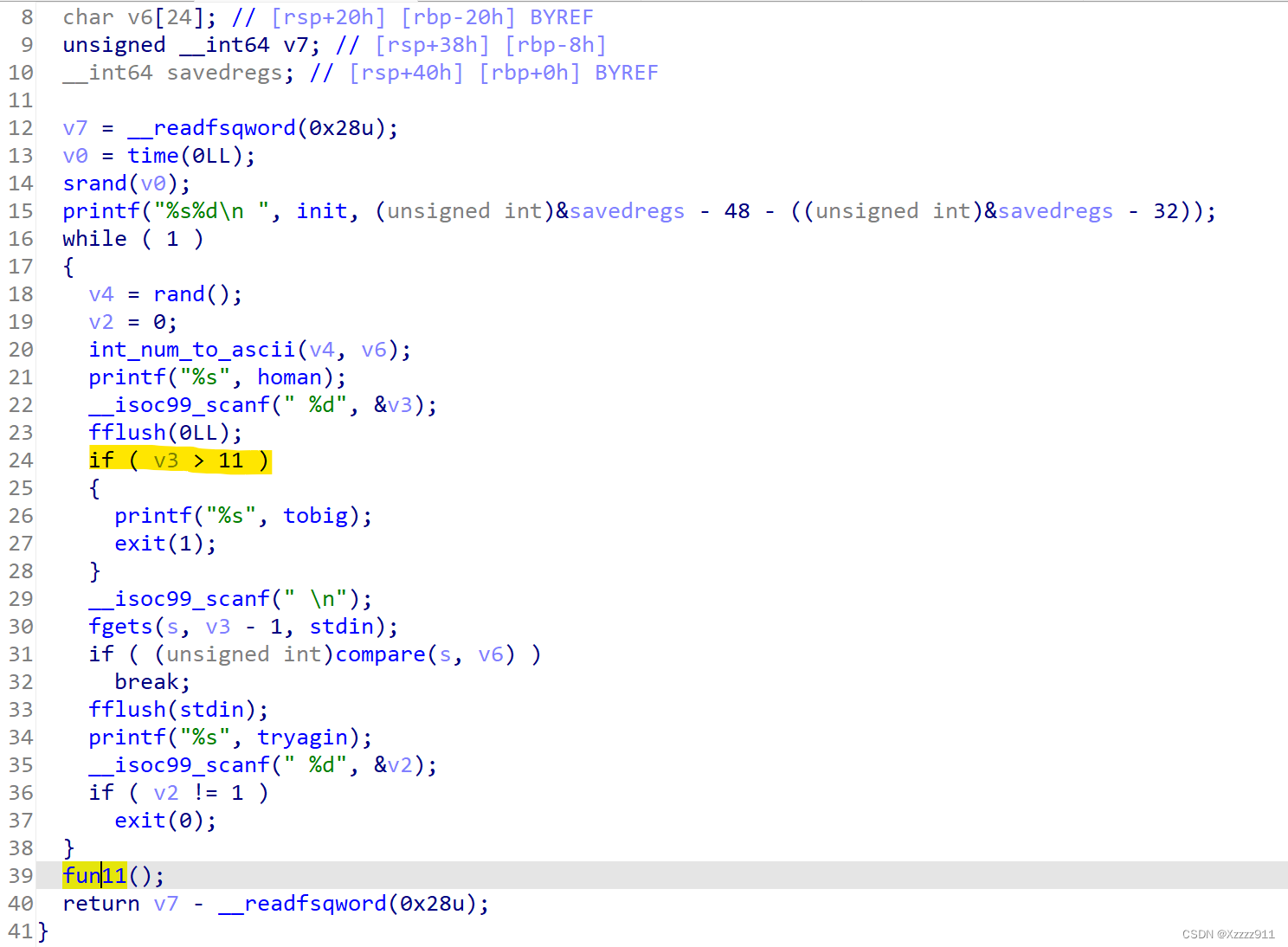
主要还得认真理清代码中的逻辑,这样才好解决问题
exp如下:
from pwn import * |
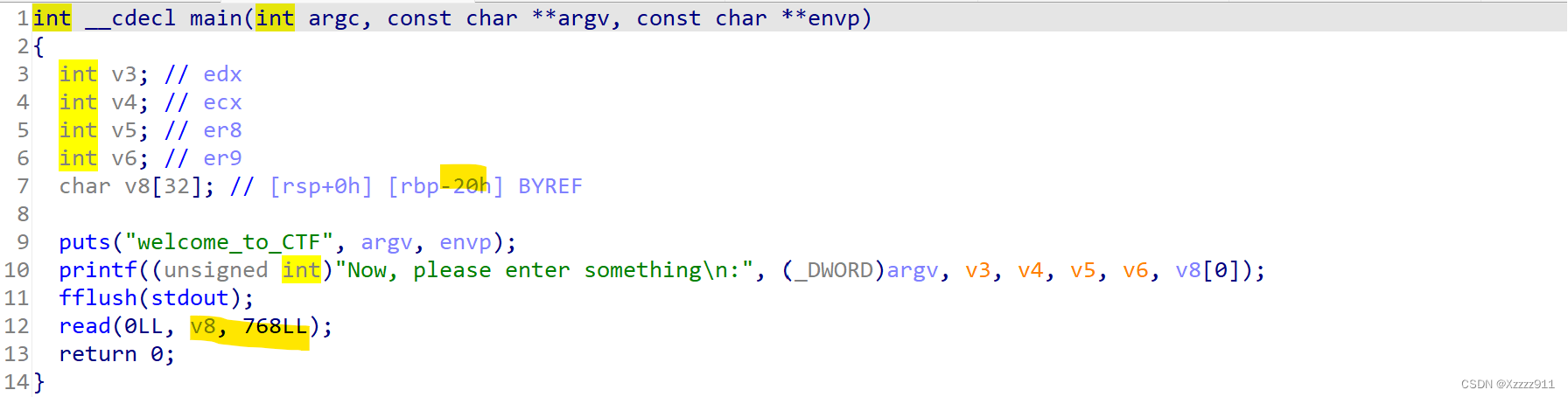
ropchain
查看一下保护机制,64位打开了canary和NX,然后还是个静态链接的程序
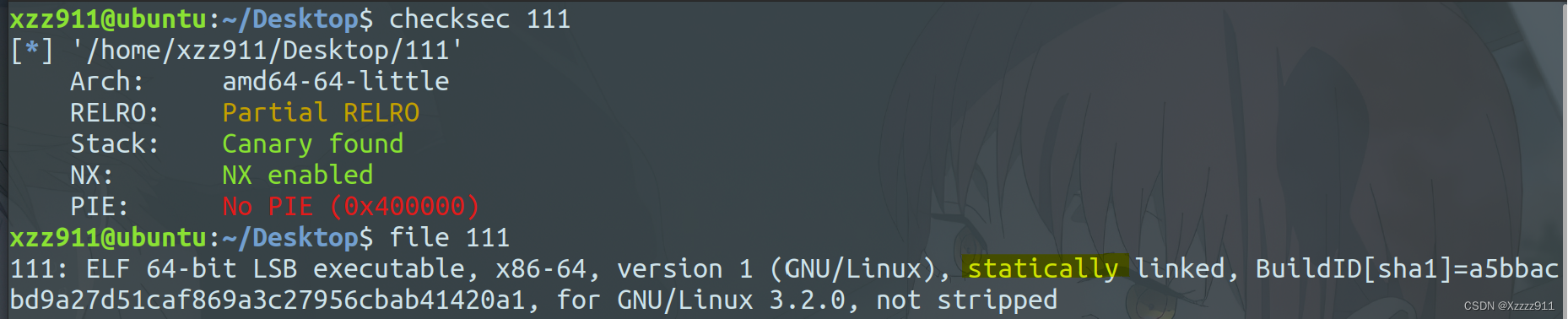
ida反汇编,观察了一下,你会发现只有read这里发生了溢出,然后又是静态链接,可以直接用ROPgadget去寻找rop执行流(不懂可看这里PWN PWN PWN !!! 技巧 (2))
使用 ROPgadget --binary 文件 --ropchain 生成构造链。
这样的话就可以直接构造payload了,exp如下:
from pwn import * |
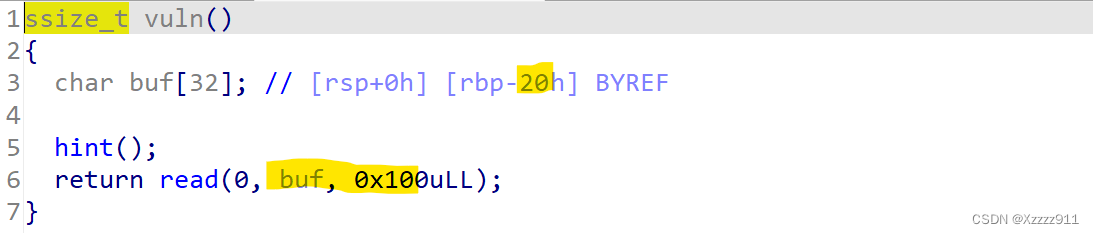
babystack
查看一下保护机制,64位打开了NX

ida反汇编一下,代码审计你会发现没有binsh和system,就发生了一个栈溢出,你就可以想到是需要用ret2libc的方法来解决,这题是通过 write 函数来泄露 libc (不懂的可以看这里,可以套用模板PWN PWN PWN !!! 技巧 (1))这里就不多讲了
exp如下:
from pwn import * |
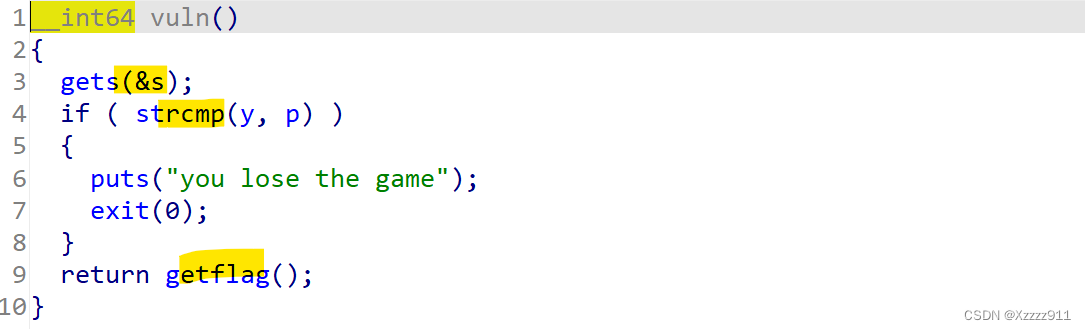
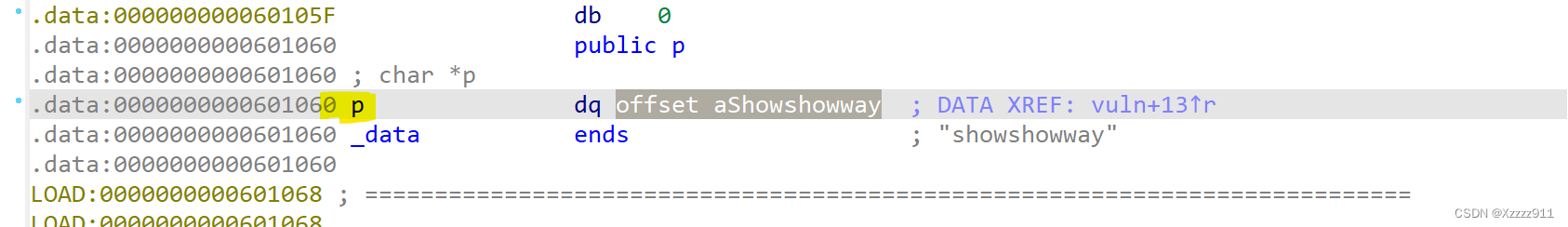
showshowway
查看一下保护机制,64位程序打开了NX

ida反汇编一下,代码审计你会发现gets函数造成了溢出,并且需要让 y 等于 p,就可以直接绕过if1语句,执行后门函数,接下来就是该怎么构造payload(s与y相距了0x40个字节,意思就是输入0x40个字节的数据就可以覆盖到 y ,然后再修改其内容,使其与p相等就可以了)这里需要认真思考,记录一下
exp如下:
from pwn import * |
pkmon
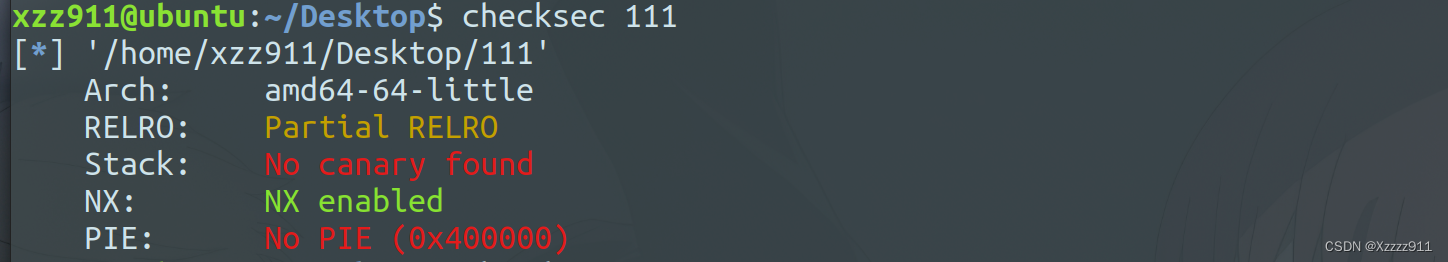
查看一下保护机制,64位程序只打开了NX
ida反汇编一下,发现有个后门函数,并且发现可以利用puts的got表地址来执行后门函数,从而获得shell
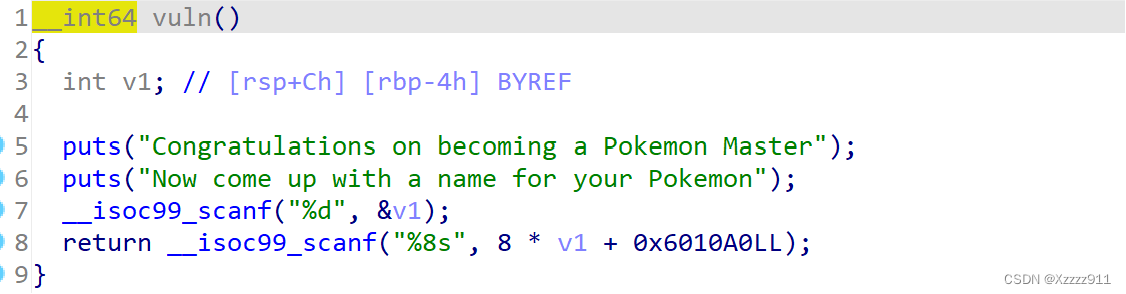
所以我们需要找到找到puts的got表地址,从而求出v1的值,这样就可以打通了

exp如下:
from pwn import * |
总结
这次比赛收获挺多的,大部分题目都是需要通过自己分析代码来解决问题,非常考验代码审计的能力,能力还得慢慢提升,加油!!!